FREE Network Assessment
Want more insight into your network?
Then sign up for a FREE Network IT Assessment.
In today’s world the computer network is the underlying engine that powers most businesses. It’s critical that the computer network function properly to allow the company to achieve its mission. Without it company operations could be brought to a complete halt.
But unless you’re in the IT industry you’re probably not thinking about the underlying components that make up your company’s IT infrastructure. As a result, if something breaks you may not know where to start when troubleshooting a problem. This is where a Network IT Assessment from Spartan Networks can help.
An “IT Assessment” is, in simple terms, a thorough analysis and review of a company’s computer network. It’s a way to take inventory of everything that exists on the network and document it for future reference or to show proof of compliance with certain federal laws like HIPAA and PCI DSS.
With an IT assessment from Spartan Networks you’ll have a full understanding of exactly what exists on your network, where the weaknesses are, and how to remediate them. After running an initial assessment of your network we’ll follow it up by implementing a risk management plan that will help identify and remediate issues over time as they come up. Our IT assessments also include detailed reports that show exactly what the problem was and how we fixed it.
The goal, over time, is to build a stronger security posture for your business and increase network uptime so that you can stay on mission.
Want more insight into your network?
Then sign up for a FREE Network IT Assessment.
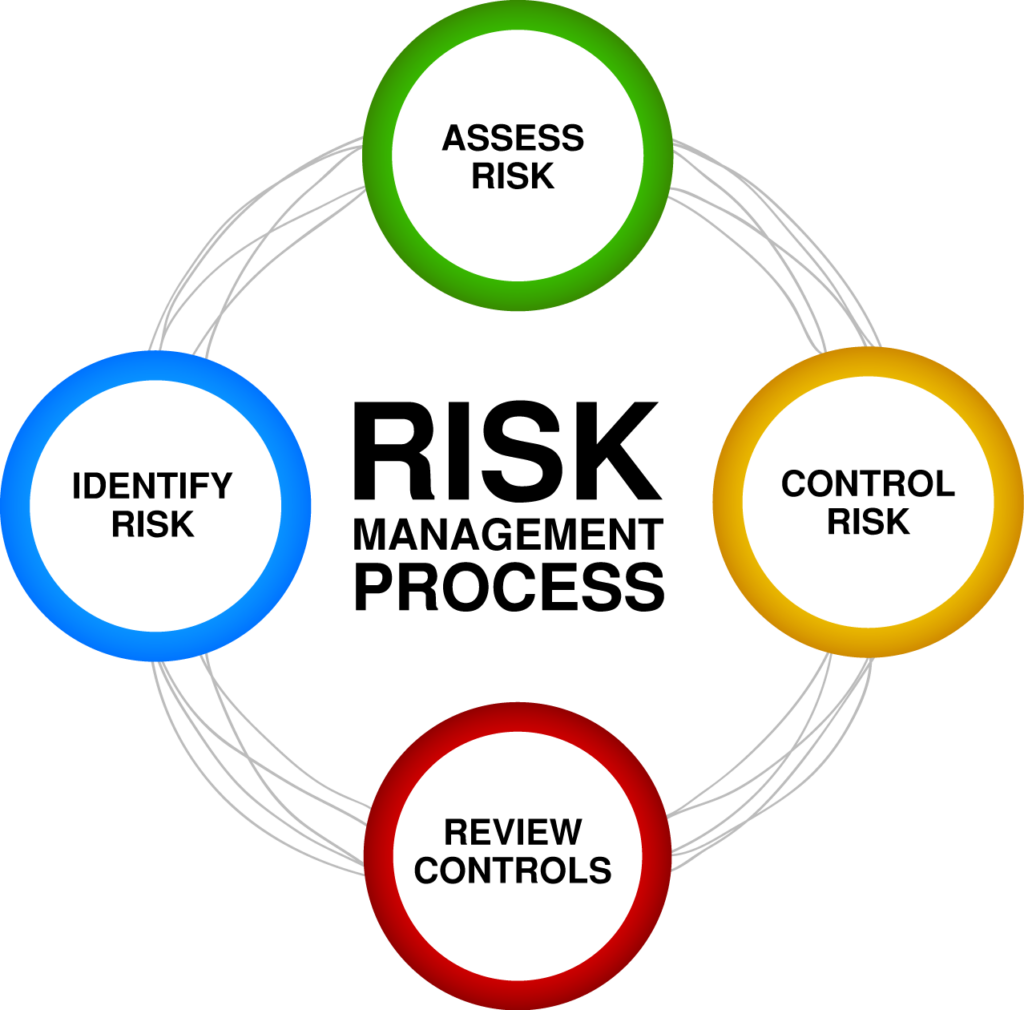
We approach the IT Assessment process from a wholistic point of view. Our Risk Management Process begins with an initial assessment of your network and concludes with an onsite quarterly review of our findings and actions taken. Using a baseline assessment of your network and subsequent follow up assessments we are able to create and implement a risk management plan that allows us to identify, manage, mitigate, and remediate risks over time. After the completion of each assessment we deliver detailed reports that identify detected risks and what actions our technicians took to manage, mitigate, or remediate them.
Conduct Initial Assessment
Someone from our team will arrive onsite to perform the initial data collection process. During this time we’ll run our proprietary data collection software which will automate the collection of information about your network. While the data collection is running we’ll spend time learning more about the physical layout of your office and answer any questions you may have. After our initial data collection we’ll begin building reports that will be delivered to you during our return meeting.
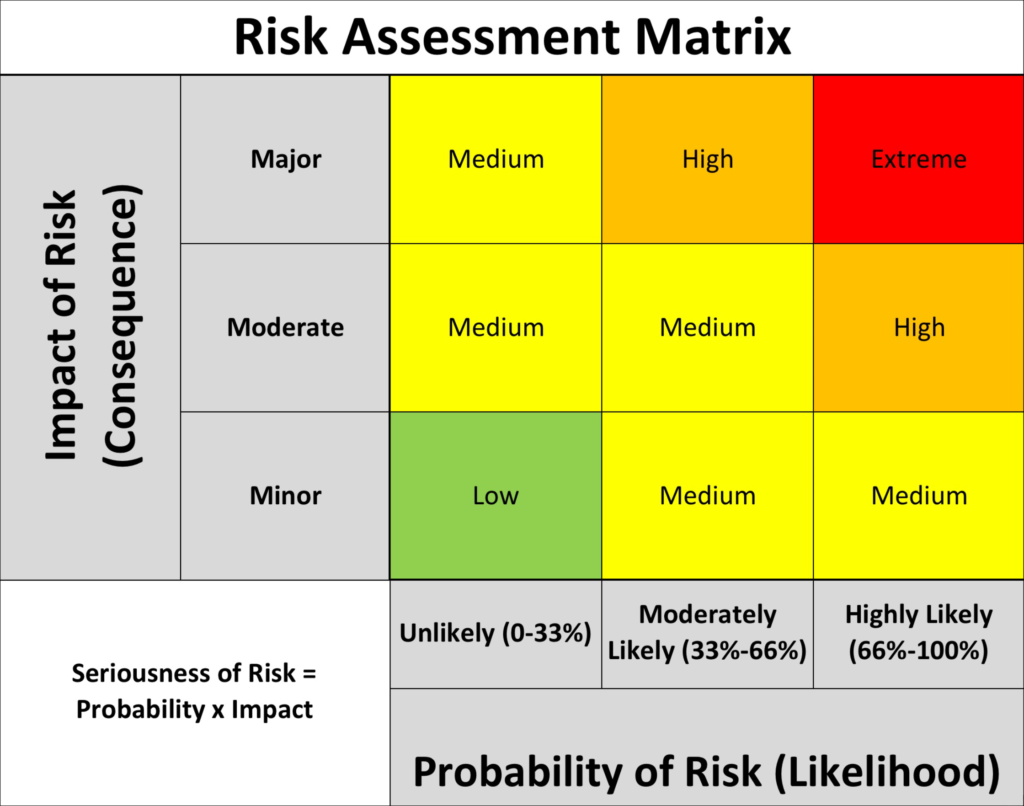
Triage Risks [Critical / High / Medium / Low]
During our return meeting we’ll begin to review the reports from our initial data collection which will serve as our baseline analysis. Each risk documented in our reports will be assigned a “triage value” of Critical, High, Medium, or Low. Our method of Risk Assessment will provide a solid foundation from which to begin work on resolving and/or mitigating each risk moving forward.
Risk scores are calculated based on the threat level of a specific risk and the probability that the risk will be exploited. Any risk deemed critical in nature will be prioritized for immediate attention as these risks indicate a potential imminent threat to your organization.
Implement Risk Management Plan & Perform Ongoing Assessments
Once we have a firm grasp of what risks and vulnerabilities exist on your network we then go into remediation mode and begin resolving those issues. As noted earlier all Critical level risks will be addressed first. Then, using our Risk Management Plan, we’ll continue resolving issues that require action. Those items that do not require action, or are designated an “acceptable risk”, will be documented and noted in future assessments moving forward.
Documentation is a key part of the assessment process and will ensure that in the event of an audit you are equipped with information that will allow you to offer Proof of Compliance Efforts to the auditor. That alone will help lower any potential fines that may be assessed against your organization if you are found to be in violation.
Quarterly Business Reviews
The final piece of the Risk Assessment Life Cycle is the Quarterly Business Review (QBR). The QBR is a once per quarter onsite review of everything that has changed on your network over the past 3 months or since the last IT assessment was completed. You can think of it as a State of the Union Address, so to speak, as it relates to the health and security of your IT infrastructure.
The QBR is an important part of a complete IT assessment process and it’s designed to let us know how well our security controls are working towards strengthening your company’s security posture.
During the QBR we meet with you (typically the CTO, CIO, CISO, or IT Director) and your team to discuss what we found, how we resolved it, and what items still require work. The Risk Assessment Process is a living process, meaning it has a beginning but no definite end. Sure, there are 4 steps to our process but after the Quarterly Business Review has taken place we rotate back to Step 1 and start all over again. The purpose of this process is to increase your company’s security posture over time and make your organization stronger, safer, and harder to break into.
That protects your business and provides you and your team with ultimate peace of mind!
Want more insight into your network?
Then sign up for a FREE Network IT Assessment.
If your business is in an industry subject to compliance regulations and standards such as HIPAA or PCI DSS then you’ll definitely want to learn more about our solutions for compliance. [Learn More …]
“What Every Business Owner Must Know About Protecting And Preserving Their Network”
We hate spam a thousand times more than you do and promise never to send you any. We also won’t sell your information or provide it to 3rd parties. See our Privacy Policy.
Spartan Networks LLC
6060 N. Central Expressway
Suite 500
Dallas, TX 75206
Phone: (214) 227-8679

Spartan Networks LLC is a Managed IT Services Provider (MSP) based in Dallas, Texas. We provide security-focused Managed IT Services to Small & Medium Enterprises (SME). Our offices are located in Dallas, Texas but we have the ability to serve businesses across the United States. No matter where you are we can support your business. It’s the 21st century and, thanks to some amazing technologies, physical business location is almost totally irrelevant.